-->
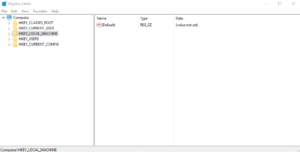
Dec 31, 2020 The Windows Registry Editor window should open and look similar to the example shown below. How to browse the Windows registry When most users need to edit their registry, they're given the location or path of where the registry value is located and what to change.
Applies to: Windows Server (Semi-Annual Channel), Windows Server 2019, Windows Server 2016, Windows 10
This article explains the supported registry setting information for the Windows implementation of the Transport Layer Security (TLS) protocol and the Secure Sockets Layer (SSL) protocol through the Schannel Security Support Provider (SSP). The registry subkeys and entries covered in this topic help you administer and troubleshoot the Schannel SSP, specifically the TLS and SSL protocols.
- Free Registry Editor is a lightweight and easy to work with piece of software whose main function resides in helping you browse, manage, change and backup your system registry, also allowing you.
- Feb 18, 2019 To edit the Registry, we use the built-in Registry Editor or regedit. It displays a tree-like navigation structure. The topmost is your computer, followed by a list of folders, and subfolders.
Caution
This information is provided as a reference to use when you are troubleshooting or verifying that the required settings are applied.We recommend that you do not directly edit the registry unless there is no other alternative.Modifications to the registry are not validated by the Registry Editor or by the Windows operating system before they are applied.As a result, incorrect values can be stored, and this can result in unrecoverable errors in the system.When possible, instead of editing the registry directly, use Group Policy or other Windows tools such as the Microsoft Management Console (MMC).If you must edit the registry, use extreme caution.
CertificateMappingMethods
This entry does not exist in the registry by default. The default value is that all four certificate mapping methods, listed below, are supported.
When a server application requires client authentication, Schannel automatically attempts to map the certificate that is supplied by the client computer to a user account. You can authenticate users who sign in with a client certificate by creating mappings, which relate the certificate information to a Windows user account. After you create and enable a certificate mapping, each time a client presents a client certificate, your server application automatically associates that user with the appropriate Windows user account.
In most cases, a certificate is mapped to a user account in one of two ways:
- A single certificate is mapped to a single user account (one-to-one mapping).
- Multiple certificates are mapped to one user account (many-to-one mapping).
By default, the Schannel provider will use the following four certificate mapping methods, listed in order of preference:
- Kerberos service-for-user (S4U) certificate mapping
- User principal name mapping
- One-to-one mapping (also known as subject/issuer mapping)
- Many-to-one mapping
Applicable versions: As designated in the Applies To list at the beginning of this topic.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
Ciphers
TLS/SSL ciphers should be controlled by configuring the cipher suite order. For details, see Configuring TLS Cipher Suite Order.
For information about default cipher suites order that are used by the Schannel SSP, see Cipher Suites in TLS/SSL (Schannel SSP).
CipherSuites
Configuring TLS/SSL cipher suites should be done using group policy, MDM or PowerShell, see Configuring TLS Cipher Suite Order for details.
For information about default cipher suites order that are used by the Schannel SSP, see Cipher Suites in TLS/SSL (Schannel SSP).
ClientCacheTime
This entry controls the amount of time that the operating system takes in milliseconds to expire client-side cache entries.A value of 0 turns off secure-connection caching.This entry does not exist in the registry by default.
The first time a client connects to a server through the Schannel SSP, a full TLS/SSL handshake is performed.When this is complete, the master secret, cipher suite, and certificates are stored in the session cache on the respective client and server.
Beginning with Windows Server 2008 and Windows Vista, the default client cache time is 10 hours.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
EnableOcspStaplingForSni
Online Certificate Status Protocol (OCSP) stapling enables a web server, such as Internet Information Services (IIS), to provide the current revocation status of a server certificate when it sends the server certificate to a client during the TLS handshake.This feature reduces the load on OCSP servers because the web server can cache the current OCSP status of the server certificate and send it to multiple web clients.Without this feature, each web client would try to retrieve the current OCSP status of the server certificate from the OCSP server.This would generate a high load on that OCSP server.
In addition to IIS, web services over http.sys can also benefit from this setting, including Active Directory Federation Services (AD FS) and Web Application Proxy (WAP).
By default, OCSP support is enabled for IIS websites that have a simple secure (SSL/TLS) binding.However, this support is not enabled by default if the IIS website is using either or both of the following types of SSL/TLS bindings:
- Require Server Name Indication
- Use Centralized Certificate Store
In this case, the server hello response during the TLS handshake won't include an OCSP stapled status by default.This behavior improves performance: The Windows OCSP stapling implementation scales to hundreds of server certificates.Because SNI and CCS enable IIS to scale to thousands of websites that potentially have thousands of server certificates, setting this behavior to be enabled by default may cause performance issues.
Applicable versions: All versions beginning with Windows Server 2012 and Windows 8.
Registry path: [HKEY_LOCAL_MACHINESYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL]
Add the following key:
'EnableOcspStaplingForSni'=dword:00000001
To disable, set the DWORD value to 0:
'EnableOcspStaplingForSni'=dword:00000000
Note
Enabling this registry key has a potential performance impact.

FIPSAlgorithmPolicy
This entry controls Federal Information Processing (FIPS) compliance.The default is 0.
Applicable versions: All versions beginning with Windows Server 2012 and Windows 8.
Registry path: HKLM SYSTEMCurrentControlSetControlLSA
Windows Server FIPS cipher suites: See Supported Cipher Suites and Protocols in the Schannel SSP.
Hashes
TLS/SSL hash algorithms should be controlled by configuring the cipher suite order.See Configuring TLS Cipher Suite Order for details.
IssuerCacheSize
This entry controls the size of the issuer cache, and it is used with issuer mapping.The Schannel SSP attempts to map all of the issuers in the client's certificate chain, not just the direct issuer of the client certificate.When the issuers don't map to an account, which is the typical case, the server might attempt to map the same issuer name repeatedly, hundreds of times per second.
Registry Editor Commands
To prevent this, the server has a negative cache, so if an issuer name does not map to an account, it is added to the cache and the Schannel SSP will not attempt to map the issuer name again until the cache entry expires.This registry entry specifies the cache size.This entry does not exist in the registry by default.The default value is 100.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
IssuerCacheTime
This entry controls the length of the cache timeout interval in milliseconds.The Schannel SSP attempts to map all of the issuers in the client's certificate chain, not just the direct issuer of the client certificate.In the case where the issuers don't map to an account, which is the typical case, the server might attempt to map the same issuer name repeatedly, hundreds of times per second.
To prevent this, the server has a negative cache, so if an issuer name doesn't map to an account, it is added to the cache and the Schannel SSP will not attempt to map the issuer name again until the cache entry expires.This cache is kept for performance reasons, so that the system does not continue trying to map the same issuers.This entry does not exist in the registry by default.The default value is 10 minutes.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
KeyExchangeAlgorithm - Client RSA key sizes
This entry controls the client RSA key sizes.
Use of key exchange algorithms should be controlled by configuring the cipher suite order.

Added in Windows 10, version 1507 and Windows Server 2016.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELKeyExchangeAlgorithmsPKCS
To specify a minimum supported range of RSA key bit length for the TLS client, create a ClientMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 1024 bits will be the minimum.
To specify a maximum supported range of RSA key bit length for the TLS client, create a ClientMaxKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, then a maximum is not enforced.

KeyExchangeAlgorithm - Diffie-Hellman key sizes
This entry controls the Diffie-Hellman key sizes.
Use of key exchange algorithms should be controlled by configuring the cipher suite order.
Added in Windows 10, version 1507 and Windows Server 2016.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELKeyExchangeAlgorithmsDiffie-Hellman
To specify a minimum supported range of Diffie-Helman key bit length for the TLS client, create a ClientMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 1024 bits will be the minimum.
To specify a maximum supported range of Diffie-Helman key bit length for the TLS client, create a ClientMaxKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, then a maximum is not enforced.
To specify the Diffie-Helman key bit length for the TLS server default, create a ServerMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 2048 bits will be the default.
MaximumCacheSize
This entry controls the maximum number of cache elements.Setting MaximumCacheSize to 0 disables the server-side session cache and prevents reconnection.Increasing MaximumCacheSize above the default values causes Lsass.exe to consume additional memory.Each session-cache element typically requires 2 to 4 KB of memory.This entry does not exist in the registry by default.The default value is 20,000 elements.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
Messaging – fragment parsing
This entry controls the maximum allowed size of fragmented TLS handshake messages that will be accepted.Messages larger than the allowed size will not be accepted, and the TLS handshake will fail.These entries do not exist in the registry by default.
When you set the value to 0x0, fragmented messages are not processed and will cause the TLS handshake to fail.This makes TLS clients or servers on the current machine non-compliant with the TLS RFCs.
The maximum allowed size can be increased up to 2^24-1 bytes.Allowing a client or server to read and store large amounts of unverified data from the network is not a good idea and will consume additional memory for each security context.
Added in Windows 7 and Windows Server 2008 R2: An update that enables Internet Explorer in Windows XP, in Windows Vista, or in Windows Server 2008 to parse fragmented TLS/SSL handshake messages is available.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELMessaging
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS client will accept, create a MessageLimitClient entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x8000 bytes.
Registry Editor Software
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS server will accept when there is no client authentication, create a MessageLimitServer entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x4000 bytes.
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS server will accept when there is client authentication, create a MessageLimitServerClientAuth entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x8000 bytes.
SendTrustedIssuerList
This entry controls the flag that is used when the list of trusted issuers is sent.In the case of servers that trust hundreds of certification authorities for client authentication, there are too many issuers for the server to be able to send them all to the client computer when requesting client authentication.In this situation, this registry key can be set, and instead of sending a partial list, the Schannel SSP will not send any list to the client.
Not sending a list of trusted issuers might impact what the client sends when it is asked for a client certificate.For example, when Internet Explorer receives a request for client authentication, it only displays the client certificates that chain up to one of the certification authorities that is sent by the server.If the server did not send a list, Internet Explorer displays all of the client certificates that are installed on the client.
This behavior might be desirable.For example, when PKI environments include cross certificates, the client and server certificates will not have the same root CA; therefore, Internet Explorer cannot chose a certificate that chains up to one of the server's CAs.By configuring the server to not send a trusted issuer list, Internet Explorer will send all its certificates.
This entry does not exist in the registry by default.
Default Send Trusted Issuer List behavior
| Windows version | Default behavior |
|---|---|
| Windows Server 2012 and Windows 8 and later | FALSE |
| Windows Server 2008 R2 and Windows 7 and earlier | TRUE |
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
ServerCacheTime
This entry controls the amount of time in milliseconds that the operating system takes to expire server-side cache entries.A value of 0 disables the server-side session cache and prevents reconnection.Increasing ServerCacheTime above the default values causes Lsass.exe to consume additional memory.Each session cache element typically requires 2 to 4 KB of memory.This entry does not exist in the registry by default.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
Default server cache time: 10 hours
TLS, DTLS, and SSL protocol version settings
Schannel SSP implements versions of the TLS, DTLS, and SSL protocols. Different Windows releases support different protocol versions. The set of (D)TLS and SSL versions available system-wide can be restricted (but not expanded) by SSPI callers specifying either SCH_CREDENTIALS or SCHANNEL_CRED structure in the AcquireCredentialsHandle call. It is recommended that SSPI callers use the system defaults, rather than imposing protocol version restrictions.
A supported (D)TLS or SSL protocol version can exist in one of the following states:
- Enabled: unless the SSPI caller explicitly disables this protocol version using the SCH_CREDENTIALS structure, Schannel SSP may negotiate this protocol version with a supporting peer.
- Disabled by default: unless the SSPI caller explicitly requests this protocol version using the deprecated SCHANNEL_CRED structure, Schannel SSP will not negotiate this protocol version.
- Disabled: Schannel SSP will not negotiate this protocol version regardless of the settings the SSPI caller may specify.
The system administrator can override the default (D)TLS and SSL protocol version settings by creating DWORD registry values 'Enabled' and 'DisabledByDefault'. These registry values are configured separately for the protocol client and server roles under the registry subkeys named using the following format:
.
These version-specific subkeys can be created under the following registry path:
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocols
For example, here are some valid registry paths with version-specific subkeys:
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsSSL 3.0Client
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsTLS 1.2Server
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsDTLS 1.2Client
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Enabled state, create a DWORD registry value named 'Enabled' with a non-zero value, and a DWORD registry value named 'DisabledByDefault' with a value of zero, under the corresponding version-specific subkey.
The following example shows TLS 1.0 client set to the Enabled state:
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Disabled by default state, create DWORD registry values named 'Enabled'and 'DisabledByDefault' with a non-zero value under the corresponding version-specific subkey. The following example shows TLS 1.0 server set to the Disabled by default state:
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Disabled state, create a DWORD registry value named 'Enabled', with a value of zero,under the corresponding version-specific subkey. The following example shows TLS 1.0 server set to the Disabled state:
Switching a (D)TLS or SSL protocol version to Disabled by default or Disabled state may causeAcquireCredentialsHandle calls to fail due to the lack of protocol versionsenabled system-wide and at the same time allowed by particular SSPI callers. In addition, reducing the set of Enabled (D)TLS and SSL versions may break interoperabilitywith remote peers.
Once the (D)TLS or SSL protocol version settings have been modified, they take effect on connections established using credential handles opened by subsequentAcquireCredentialsHandle calls. (D)TLS and SSL client and server applicationsand services tend to reuse credential handles for multiple connections, for performance reasons. In order to get these applications to reacquire their credential handles,an application or service restart may be required.
Please note that these registry settings only apply to Schannel SSP and do not affect any third-party (D)TLS and SSL implementations that may be installed on the system.
If Operating Systems weren't flexible, we would not be talking about registry editors today. Look at this way: wouldn't computers be boring if there weren't ways to manipulate them to suit your style and preferences? For most people, including me, computers would definitely be boring. However, we know for a fact that one can configure their Operating Systems their own way, and there are many software that you can use to do this. The solutions are known as registry editors.
Related:
FIPSAlgorithmPolicy
This entry controls Federal Information Processing (FIPS) compliance.The default is 0.
Applicable versions: All versions beginning with Windows Server 2012 and Windows 8.
Registry path: HKLM SYSTEMCurrentControlSetControlLSA
Windows Server FIPS cipher suites: See Supported Cipher Suites and Protocols in the Schannel SSP.
Hashes
TLS/SSL hash algorithms should be controlled by configuring the cipher suite order.See Configuring TLS Cipher Suite Order for details.
IssuerCacheSize
This entry controls the size of the issuer cache, and it is used with issuer mapping.The Schannel SSP attempts to map all of the issuers in the client's certificate chain, not just the direct issuer of the client certificate.When the issuers don't map to an account, which is the typical case, the server might attempt to map the same issuer name repeatedly, hundreds of times per second.
Registry Editor Commands
To prevent this, the server has a negative cache, so if an issuer name does not map to an account, it is added to the cache and the Schannel SSP will not attempt to map the issuer name again until the cache entry expires.This registry entry specifies the cache size.This entry does not exist in the registry by default.The default value is 100.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
IssuerCacheTime
This entry controls the length of the cache timeout interval in milliseconds.The Schannel SSP attempts to map all of the issuers in the client's certificate chain, not just the direct issuer of the client certificate.In the case where the issuers don't map to an account, which is the typical case, the server might attempt to map the same issuer name repeatedly, hundreds of times per second.
To prevent this, the server has a negative cache, so if an issuer name doesn't map to an account, it is added to the cache and the Schannel SSP will not attempt to map the issuer name again until the cache entry expires.This cache is kept for performance reasons, so that the system does not continue trying to map the same issuers.This entry does not exist in the registry by default.The default value is 10 minutes.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
KeyExchangeAlgorithm - Client RSA key sizes
This entry controls the client RSA key sizes.
Use of key exchange algorithms should be controlled by configuring the cipher suite order.
Added in Windows 10, version 1507 and Windows Server 2016.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELKeyExchangeAlgorithmsPKCS
To specify a minimum supported range of RSA key bit length for the TLS client, create a ClientMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 1024 bits will be the minimum.
To specify a maximum supported range of RSA key bit length for the TLS client, create a ClientMaxKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, then a maximum is not enforced.
KeyExchangeAlgorithm - Diffie-Hellman key sizes
This entry controls the Diffie-Hellman key sizes.
Use of key exchange algorithms should be controlled by configuring the cipher suite order.
Added in Windows 10, version 1507 and Windows Server 2016.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELKeyExchangeAlgorithmsDiffie-Hellman
To specify a minimum supported range of Diffie-Helman key bit length for the TLS client, create a ClientMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 1024 bits will be the minimum.
To specify a maximum supported range of Diffie-Helman key bit length for the TLS client, create a ClientMaxKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, then a maximum is not enforced.
To specify the Diffie-Helman key bit length for the TLS server default, create a ServerMinKeyBitLength entry.This entry does not exist in the registry by default.After you have created the entry, change the DWORD value to the desired bit length.If not configured, 2048 bits will be the default.
MaximumCacheSize
This entry controls the maximum number of cache elements.Setting MaximumCacheSize to 0 disables the server-side session cache and prevents reconnection.Increasing MaximumCacheSize above the default values causes Lsass.exe to consume additional memory.Each session-cache element typically requires 2 to 4 KB of memory.This entry does not exist in the registry by default.The default value is 20,000 elements.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
Messaging – fragment parsing
This entry controls the maximum allowed size of fragmented TLS handshake messages that will be accepted.Messages larger than the allowed size will not be accepted, and the TLS handshake will fail.These entries do not exist in the registry by default.
When you set the value to 0x0, fragmented messages are not processed and will cause the TLS handshake to fail.This makes TLS clients or servers on the current machine non-compliant with the TLS RFCs.
The maximum allowed size can be increased up to 2^24-1 bytes.Allowing a client or server to read and store large amounts of unverified data from the network is not a good idea and will consume additional memory for each security context.
Added in Windows 7 and Windows Server 2008 R2: An update that enables Internet Explorer in Windows XP, in Windows Vista, or in Windows Server 2008 to parse fragmented TLS/SSL handshake messages is available.
Registry path: HKLMSYSTEMCurrentControlSetControlSecurityProvidersSCHANNELMessaging
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS client will accept, create a MessageLimitClient entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x8000 bytes.
Registry Editor Software
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS server will accept when there is no client authentication, create a MessageLimitServer entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x4000 bytes.
To specify a maximum allowed size of fragmented TLS handshake messages that the TLS server will accept when there is client authentication, create a MessageLimitServerClientAuth entry.After you have created the entry, change the DWORD value to the desired bit length.If not configured, the default value will be 0x8000 bytes.
SendTrustedIssuerList
This entry controls the flag that is used when the list of trusted issuers is sent.In the case of servers that trust hundreds of certification authorities for client authentication, there are too many issuers for the server to be able to send them all to the client computer when requesting client authentication.In this situation, this registry key can be set, and instead of sending a partial list, the Schannel SSP will not send any list to the client.
Not sending a list of trusted issuers might impact what the client sends when it is asked for a client certificate.For example, when Internet Explorer receives a request for client authentication, it only displays the client certificates that chain up to one of the certification authorities that is sent by the server.If the server did not send a list, Internet Explorer displays all of the client certificates that are installed on the client.
This behavior might be desirable.For example, when PKI environments include cross certificates, the client and server certificates will not have the same root CA; therefore, Internet Explorer cannot chose a certificate that chains up to one of the server's CAs.By configuring the server to not send a trusted issuer list, Internet Explorer will send all its certificates.
This entry does not exist in the registry by default.
Default Send Trusted Issuer List behavior
| Windows version | Default behavior |
|---|---|
| Windows Server 2012 and Windows 8 and later | FALSE |
| Windows Server 2008 R2 and Windows 7 and earlier | TRUE |
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
ServerCacheTime
This entry controls the amount of time in milliseconds that the operating system takes to expire server-side cache entries.A value of 0 disables the server-side session cache and prevents reconnection.Increasing ServerCacheTime above the default values causes Lsass.exe to consume additional memory.Each session cache element typically requires 2 to 4 KB of memory.This entry does not exist in the registry by default.
Applicable versions: All versions beginning with Windows Server 2008 and Windows Vista.
Registry path: HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNEL
Default server cache time: 10 hours
TLS, DTLS, and SSL protocol version settings
Schannel SSP implements versions of the TLS, DTLS, and SSL protocols. Different Windows releases support different protocol versions. The set of (D)TLS and SSL versions available system-wide can be restricted (but not expanded) by SSPI callers specifying either SCH_CREDENTIALS or SCHANNEL_CRED structure in the AcquireCredentialsHandle call. It is recommended that SSPI callers use the system defaults, rather than imposing protocol version restrictions.
A supported (D)TLS or SSL protocol version can exist in one of the following states:
- Enabled: unless the SSPI caller explicitly disables this protocol version using the SCH_CREDENTIALS structure, Schannel SSP may negotiate this protocol version with a supporting peer.
- Disabled by default: unless the SSPI caller explicitly requests this protocol version using the deprecated SCHANNEL_CRED structure, Schannel SSP will not negotiate this protocol version.
- Disabled: Schannel SSP will not negotiate this protocol version regardless of the settings the SSPI caller may specify.
The system administrator can override the default (D)TLS and SSL protocol version settings by creating DWORD registry values 'Enabled' and 'DisabledByDefault'. These registry values are configured separately for the protocol client and server roles under the registry subkeys named using the following format:
.
These version-specific subkeys can be created under the following registry path:
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocols
For example, here are some valid registry paths with version-specific subkeys:
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsSSL 3.0Client
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsTLS 1.2Server
HKLM SYSTEMCurrentControlSetControlSecurityProvidersSCHANNELProtocolsDTLS 1.2Client
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Enabled state, create a DWORD registry value named 'Enabled' with a non-zero value, and a DWORD registry value named 'DisabledByDefault' with a value of zero, under the corresponding version-specific subkey.
The following example shows TLS 1.0 client set to the Enabled state:
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Disabled by default state, create DWORD registry values named 'Enabled'and 'DisabledByDefault' with a non-zero value under the corresponding version-specific subkey. The following example shows TLS 1.0 server set to the Disabled by default state:
In order to override a system default and set a supported (D)TLS or SSL protocol version to the Disabled state, create a DWORD registry value named 'Enabled', with a value of zero,under the corresponding version-specific subkey. The following example shows TLS 1.0 server set to the Disabled state:
Switching a (D)TLS or SSL protocol version to Disabled by default or Disabled state may causeAcquireCredentialsHandle calls to fail due to the lack of protocol versionsenabled system-wide and at the same time allowed by particular SSPI callers. In addition, reducing the set of Enabled (D)TLS and SSL versions may break interoperabilitywith remote peers.
Once the (D)TLS or SSL protocol version settings have been modified, they take effect on connections established using credential handles opened by subsequentAcquireCredentialsHandle calls. (D)TLS and SSL client and server applicationsand services tend to reuse credential handles for multiple connections, for performance reasons. In order to get these applications to reacquire their credential handles,an application or service restart may be required.
Please note that these registry settings only apply to Schannel SSP and do not affect any third-party (D)TLS and SSL implementations that may be installed on the system.
If Operating Systems weren't flexible, we would not be talking about registry editors today. Look at this way: wouldn't computers be boring if there weren't ways to manipulate them to suit your style and preferences? For most people, including me, computers would definitely be boring. However, we know for a fact that one can configure their Operating Systems their own way, and there are many software that you can use to do this. The solutions are known as registry editors.
Related:
Registrar
Registrar is a robust solution that allows you to maintain your registry as well as the registry of your network. Not only was this software dubbed the expert in registry management during launch, it still stand to be the game changer today. Features include fast background search and replace, bookmark editing with categories and registries restoration.
Regalyzer
Regalyzer has unique features that make registry work smooth and precise. These include improved search functions, support of the 64 bit integer Q Word, support of version five filter and the new undo and redo log in .reg format. Use command line parameters to jump to key and you can even display reg content without importing.
SRE
SRE is an acronym that stands for Small Registry Editor. The software is great because it can change your registry settings, even if they are blocked by virus. Also, it doubles as the best registry, which allows you to perform blocked registry. Customers say that SRE is wonderful and it is definitely an app worth downloading.
Reg Scanner
This software can help you scan your registry, find the desired value and match the values to your search criteria. Further, the software helps you to display all your results in one list. The software also enables you to export your registry value to a .reg file, and then you can use the value in the Reg Edit tool.
JV6 Power Tool X
Use this software to get an overview of the health status of your system. People who have used the software say I is simple to use. Also, it is one such powerful tool that guarantees real results. You can use this software to increase the speed and performance of your computer. You can also find and replace data inside files and inside Windows registry.
Reg Organizer
Registry Editor Pc
Reg Organizer is used to change, streamline, and clean Windows. It is intended to easily free up framework assets and rev execution to the maximum. The software features a visual auto start administrator and a progressed uninstaller. It is best for highlighting scan for remains of the uninstalled programs.
Reg Edit X 3.0
Reg Edit X is the best software for those who are looking for a perfect editor that can make registry editing easy and productive. The software has unique features that will not only make your registry process easy, but also quick and effective. Apparently, Reg Edit X version 3.0 can be a great replacement for Windows registry because it features a crawler that works fine with Vista and Windows 7 UAC.
Reg
We've known Microsoft Registry Editor as the most popular configuration solution, but Reg is the best alternative that that you can use. The software features advanced bookmarks, improved search, simple and direct navigation and threaded search. The software was written in C++ and it supports Windows 10, XP and 7.
Registry Editor for Other Platforms
Many of the registry editors you will find online are for Windows Platform. This indicates that the probability of getting the best editor for Linux, Mac and Mac OS X cannot be close to one. Regardless, additional registry editors for windows will help you take full charge of your personal computer. Below is a list of additional registry editor software.
Regwatch
Regwatcht is being praised as a good software today. In fact, it is the easiest solution to use, and it will help you tweak your Windows Operating System within minutes, to say the least. It is missing a few features though, which means that it is not the best for advanced use. It is perfect for basic use.
Registrar Registry Manager – Home Edition
The user interface of this software is simple, the functionality is on point, and it is easy to use. There are two versions of the home edition registry: The free version and the paid software. The free version is quite basic, but it has all the basic functions that you will need for registry.
What is Registry Editor?
The habit and desire to configure Windows Operating System in our own way is nothing new. We've seen people edit the registry system using Windows Registry because they want their computers to work in a unique way – something that should not be difficult for you to do. This is the best reason that explains why Registry Editors are important.
By definition, a registry editor software is a tool built to help you editor the registry file of your computer's Operating System. There are many software that you can use today, and we have provided you with a list of the best options to choose.
How to install Registry Editor
Note that these software are all for Windows Operating System. This means that their installation procedure is a one-size-fits-all although you might find out that some have different installation instructions. I suggest that you follow the instruction provided on your screen to install the software. Installation is quick and easy; it should take you less than 10 minutes to get started.
More insight on Reg Editor
Registry Editor Xp
The advantage of using a registry editor is that you can take charge of your Windows Operating System; you can tweak it by editing the registry file and make the OS run the way you prefer. Each software solution has unique features. For example, you can search a registry, edit it, export the data to an XML file or undo the changes you made previously.
Some editors are complex while others are simple. People often go for simple ones, but you can as well try complex software if you already have experience with the basic ones.
